Ganz große Klasse!
-
Einfach großartig 👏 @back2theRoot
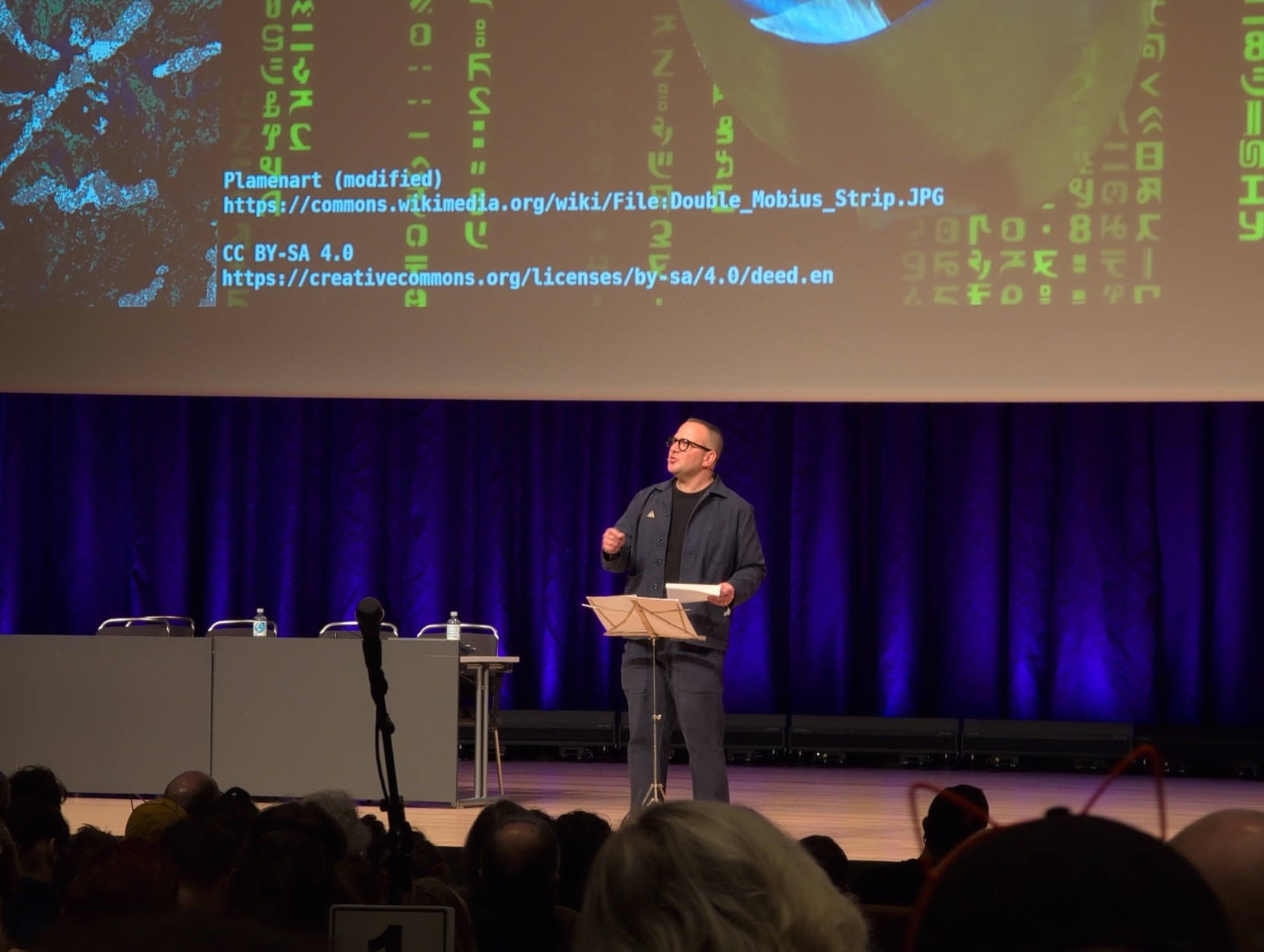
Wie Martha Root als Pink Ranger ein komplettes Neonazi-Netzwerk hackte
‚Es war eine Szene, die selbst für den Chaos Communication Congress außergewöhnlich war. Auf der Bühne: eine Person im pinkfarbenen Power-Ranger-Kostüm. Im Publikum: Tausende IT-Sicherheits-Expert:innen, Hacker:innen und Aktivist:innen aus aller Welt. Was dann folgte, war kein Show-Gag, sondern ein Live-Demonstrationsmoment digitaler Macht. Die unter dem Pseudonym „Martha Root“ bekannte Person, präsentierte öffentlich, wie sie eine rechtsextreme Dating-Plattform kompromittiert, vollständig kopiert und schließlich gelöscht hatte.‘
https://www.boah.at/wie-martha-root-als-pink-ranger-ein-komplettes-neonazi-netzwerk-hackte/
@autonomysolidarity @back2theRoot
Der Artikel erwähnt zwar, dass die Daten veröffentlicht wurden, vergisst aber leider die Adresse zu nennen:
The article mentions that the data has been published, but unfortunately fails to provide the address.
-
White Leaks
Files and user information from the white supremacist websites WhiteDate (a white supremacist dating site), WhiteChild (a white supremacist site focused on family and ancestry), and WhiteDeal (a white supremacist networking and professional development site).
https://ddosecrets.com/article/whiteleaks
Thanks to @ddosecretsSee also: https://okstupid.lol/
Spread the Word! #FightNazis
The data and findings were first presented at the 39th Chaos Communications Congress.
@olivetree deshalb auch dieser Post ☝️
-
@olivetree deshalb auch dieser Post ☝️
Ah, sehr gut.
Denn Tröt hatte ich nicht in der Timeline. Ich bin über den Link zum deutschsprachigen Artikel in den Thread gestolpert, da wurden mir nur die Tröts angezeigt, die sich auf selbigen bezogen.
-
Ah, sehr gut.
Denn Tröt hatte ich nicht in der Timeline. Ich bin über den Link zum deutschsprachigen Artikel in den Thread gestolpert, da wurden mir nur die Tröts angezeigt, die sich auf selbigen bezogen.
@olivetree alles gut, kann man ja nicht oft genug drauf hinweisen 😁
-
Hacktivist deletes white supremacist websites live onstage during hacker conference
‚A hacktivist remotely wiped three white supremacist websites live onstage during their talk at a hacker conference last week, with the sites yet to return online.
The pseudonymous hacker, who goes by Martha Root — dressed as Pink Ranger from the Power Rangers — deleted the servers of WhiteDate, WhiteChild, and WhiteDeal in real time at the end of a talk at the annual Chaos Communication Congress in Hamburg, Germany….‘Great 👏 @back2theRoot
#Ccc #39C3 #FightNazis #Hacking #Tech #Technology #Activism #HH #Hamburg #Germany
@autonomysolidarity @back2theRoot
Now do whitehouse dot gov -
White Leaks
Files and user information from the white supremacist websites WhiteDate (a white supremacist dating site), WhiteChild (a white supremacist site focused on family and ancestry), and WhiteDeal (a white supremacist networking and professional development site).
https://ddosecrets.com/article/whiteleaks
Thanks to @ddosecretsSee also: https://okstupid.lol/
Spread the Word! #FightNazis
The data and findings were first presented at the 39th Chaos Communications Congress.
How Hackers Are Fighting Back Against ICE
‚ICE has been invading U.S. cities, targeting, surveilling, harassing, assaulting, detaining, and torturing people who are undocumented immigrants. They also have targeted people with work permits, asylum seekers, permanent residents (people holding “green cards”), naturalized citizens, and even citizens by birth. ICE has spent hundreds of millions of dollars on surveillance technology to spy on anyone—and potentially everyone—in the United States. It can be hard to imagine how to defend oneself against such an overwhelming force.
But a few enterprising hackers have started projects to do counter surveillance against ICE, and hopefully protect their communities through clever use of technology….‘
https://www.eff.org/deeplinks/2026/01/how-hackers-are-fighting-back-against-ice
-
White Leaks
Files and user information from the white supremacist websites WhiteDate (a white supremacist dating site), WhiteChild (a white supremacist site focused on family and ancestry), and WhiteDeal (a white supremacist networking and professional development site).
https://ddosecrets.com/article/whiteleaks
Thanks to @ddosecretsSee also: https://okstupid.lol/
Spread the Word! #FightNazis
The data and findings were first presented at the 39th Chaos Communications Congress.
White supremacist dating site profiles linked to Tory and Reform councillors
Conservative councillor suspended after her account is included on a leaked user list from WhiteDate site.....
Thanks to @back2theRoot via https://okstupid.lol/ 👏
#WhiteLeaks #FightNazis #Hacking #Technology #UK #Tory #ReformUK
-
White supremacist dating site profiles linked to Tory and Reform councillors
Conservative councillor suspended after her account is included on a leaked user list from WhiteDate site.....
Thanks to @back2theRoot via https://okstupid.lol/ 👏
#WhiteLeaks #FightNazis #Hacking #Technology #UK #Tory #ReformUK
@autonomysolidarity @poemproducer @back2theRoot It is nicer to be a White Suprematist in a Conservative Party (until somebody is leaking the truth).
-
How Hackers Are Fighting Back Against ICE
‚ICE has been invading U.S. cities, targeting, surveilling, harassing, assaulting, detaining, and torturing people who are undocumented immigrants. They also have targeted people with work permits, asylum seekers, permanent residents (people holding “green cards”), naturalized citizens, and even citizens by birth. ICE has spent hundreds of millions of dollars on surveillance technology to spy on anyone—and potentially everyone—in the United States. It can be hard to imagine how to defend oneself against such an overwhelming force.
But a few enterprising hackers have started projects to do counter surveillance against ICE, and hopefully protect their communities through clever use of technology….‘
https://www.eff.org/deeplinks/2026/01/how-hackers-are-fighting-back-against-ice
Whistleblower drops 'largest ever' #ICE leak to unmask agents
‚A whistleblower has released the identities of approximately 4,500 ICE and Border Patrol agents, marking what may be the largest data breach in the Department of Homeland Security's history. The leak, published on ICE List, was triggered by national outrage following the fatal shooting of 37-year-old Renee Nicole Good by an ICE agent….‘
-
Whistleblower drops 'largest ever' #ICE leak to unmask agents
‚A whistleblower has released the identities of approximately 4,500 ICE and Border Patrol agents, marking what may be the largest data breach in the Department of Homeland Security's history. The leak, published on ICE List, was triggered by national outrage following the fatal shooting of 37-year-old Renee Nicole Good by an ICE agent….‘
-
Whistleblower drops 'largest ever' #ICE leak to unmask agents
‚A whistleblower has released the identities of approximately 4,500 ICE and Border Patrol agents, marking what may be the largest data breach in the Department of Homeland Security's history. The leak, published on ICE List, was triggered by national outrage following the fatal shooting of 37-year-old Renee Nicole Good by an ICE agent….‘
@autonomysolidarity
C'est le genre de truc qui arrive forcément quand la justice disfonctionne, comme c'est le cas pour ce meurtre aux US.
Certains citoyens ne l'acceptent pas, et agissent selon leurs moyens. -
@autonomysolidarity We need to make sure we get backups of all this and decentralize the list.
-
@autonomysolidarity Love the detail that they use Icelands top-level domain.
-
Whistleblower drops 'largest ever' #ICE leak to unmask agents
‚A whistleblower has released the identities of approximately 4,500 ICE and Border Patrol agents, marking what may be the largest data breach in the Department of Homeland Security's history. The leak, published on ICE List, was triggered by national outrage following the fatal shooting of 37-year-old Renee Nicole Good by an ICE agent….‘
@autonomysolidarity Jetzt bloss nicht in einer Botschaft verstecken, das geht bekanntlich nicht gut aus /s
-
https://wiki.icelist.is/index.php?title=Main_Page
"The ICE List Wiki is designed for public use. Journalists, researchers, and advocacy groups use the data to track enforcement patterns, identify repeat agencies or jurisdictions, and contextualise individual incidents. Pages may be cited with attribution."
Spread the Message!
-
https://wiki.icelist.is/index.php?title=Main_Page
"The ICE List Wiki is designed for public use. Journalists, researchers, and advocacy groups use the data to track enforcement patterns, identify repeat agencies or jurisdictions, and contextualise individual incidents. Pages may be cited with attribution."
Spread the Message!
and in the states on comcast its 403ed(FORBIDDEN).. use tor browser or brave's "new private window with tor" for access..
-
and in the states on comcast its 403ed(FORBIDDEN).. use tor browser or brave's "new private window with tor" for access..
@hotelzululima @autonomysolidarity it is working here (EU), it is just terribly slow, probably too many visitors.
-
https://wiki.icelist.is/index.php?title=Main_Page
"The ICE List Wiki is designed for public use. Journalists, researchers, and advocacy groups use the data to track enforcement patterns, identify repeat agencies or jurisdictions, and contextualise individual incidents. Pages may be cited with attribution."
Spread the Message!
@autonomysolidarity its 404ing
-
@thomkennon in which Country are you?
-
@thomkennon in which Country are you?
@autonomysolidarity US, so-called